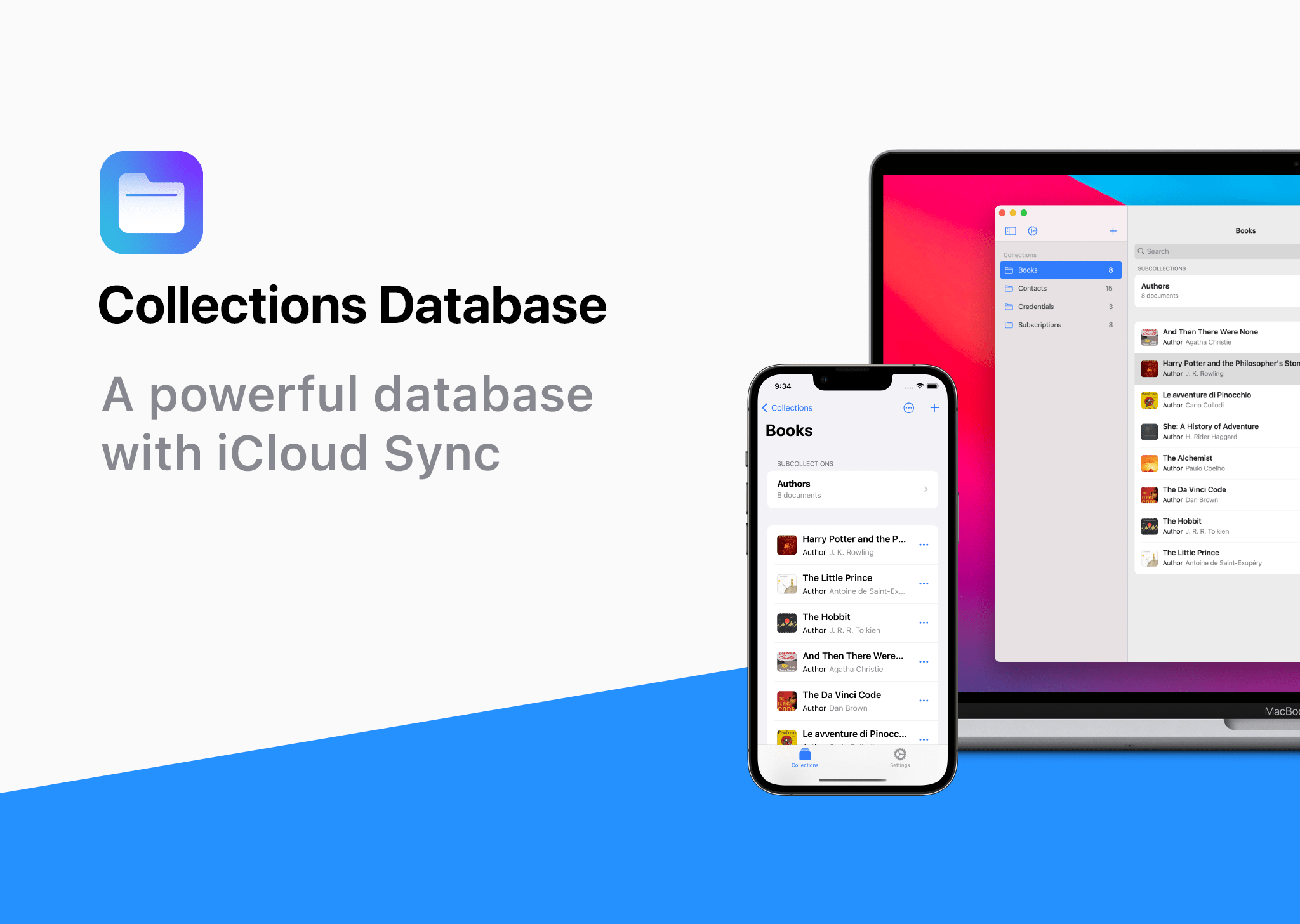
Your time is precious. So, instead of spinning your wheels as you look for the next thing to watch, read, play, or do, try Sofa for iPhone, iPad, and soon, the Vision Pro. It lets you be more intentional with your downtime by creating organized lists as you discover new things to try.
Most apps are designed for work. Sofa’s different. It’s built for play, with a focus on making the most of your free time. It’s more organized than a list in Notes, with just enough structure combined with extensive customization options to make it your own.
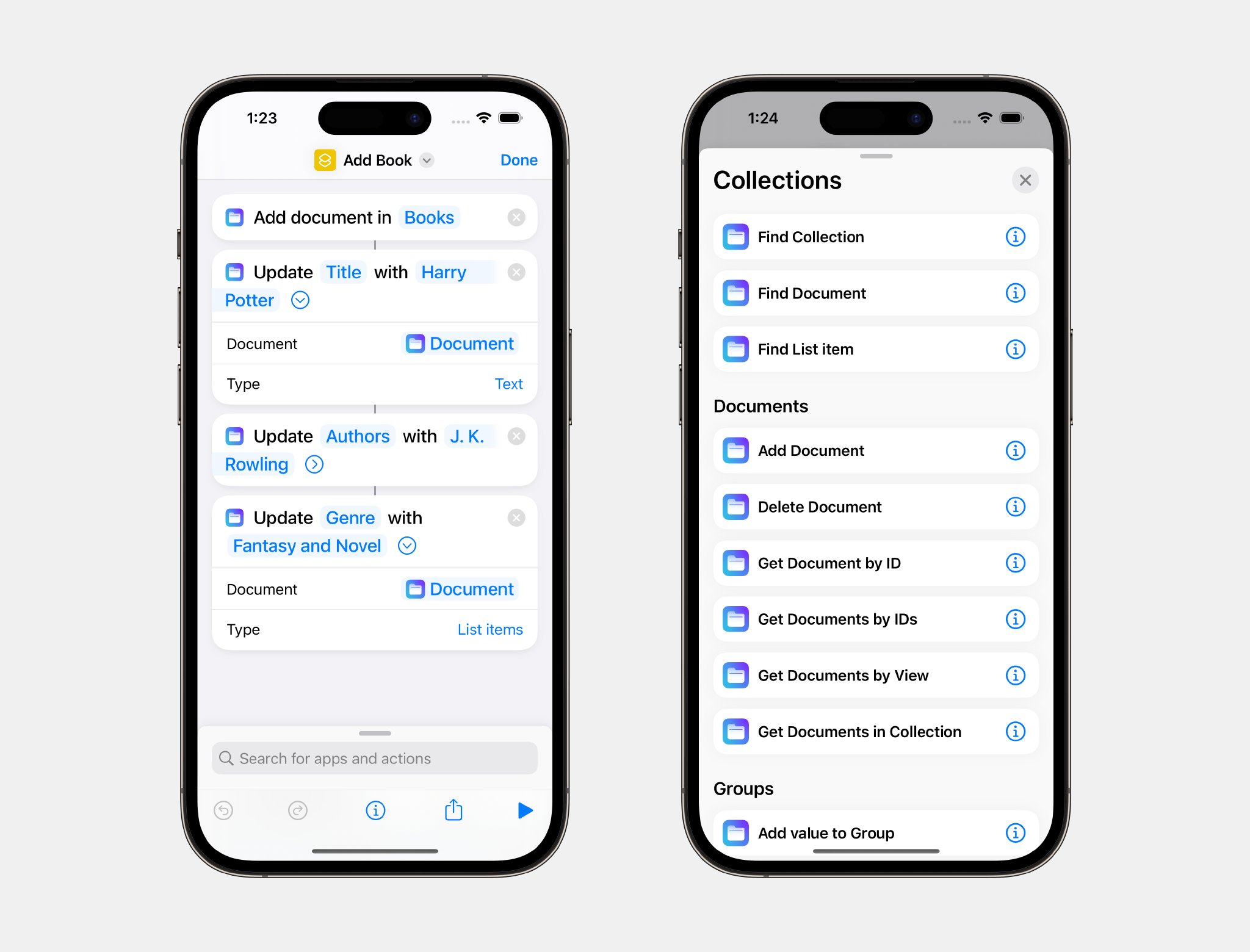
You can track anything you want in Sofa: apps, books, movies, TV shows, podcasts, YouTube videos, websites, travel ideas, restaurants, and more. The app includes over 100 themes, Shortcuts support, Smart Lists, user-defined ingredients, and more. It’s the sort of flexibility, from the lists you make to how the app looks, feels, and works, that you won’t find anywhere else.
Most of Sofa, including unlimited lists, syncing via iCloud, tracking your activity, and automating with Shortcuts is completely free. But, with a Super Sofa subscription, you can add custom ingredients, Smart Lists, item and list pinning, sticky notes, and more.
So, download Sofa today for free, and be sure to take advantage of a limited-time deal just for MacStories readers, who can get 40% off their first year of a Super Sofa subscription by going to sofahq.com/macstories.
Our thanks to Sofa for sponsoring MacStories this week.